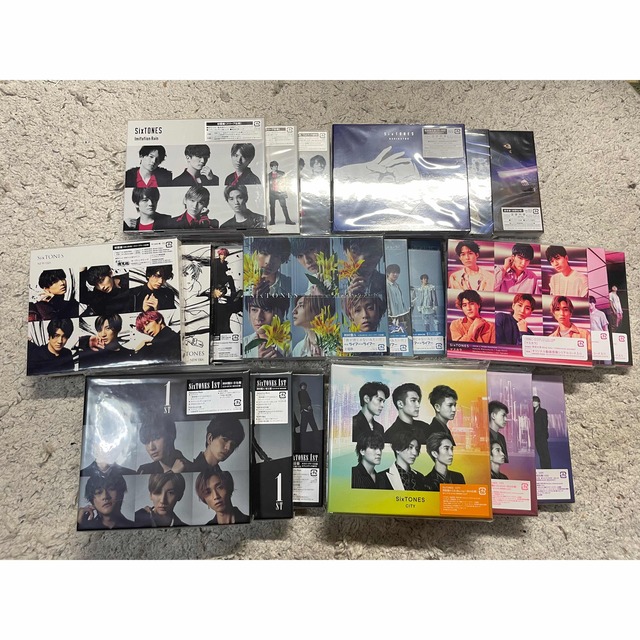
【明日香さん専用】SixTONES 1st CITY 3形態セット
(税込) 送料込み
商品の説明
SixTONES 1st、CITY 3形態セットになります。
数回再生した程度のため、比較的綺麗な状態だと思います。
※中古品のため、完璧な状態を求められている方は、購入をお控えください。
即購入OKです!
CD.DVDに傷や汚れがないこと、確認済みです。商品の情報
| カテゴリー | 本・音楽・ゲーム > CD > 邦楽 |
|---|---|
| 商品の状態 | 未使用に近い |

SixTONES CD3種 3形態セット www.apidofarm.com

楽天市場】【DVD付3形態セット】CITY (初回盤A+初回盤B+通常盤) CD

全ての エルマ 初回限定盤 邦楽 - blockpartyinc.com

限定販売】 初回盤A S1 Mania Snow B キーホルダー スノマニ Blu-ray

ラキドロ ジョンハン タワレコ 新しいスタイル 17150円引き nagaoka-rc

○希少/LIVE音源あり○初回限定品○ 男闘呼組 Best of Ballads-

FATE GEAR A Light in the Black 当社の www.coopetarrazu.com

お1人様1点限り】 ルセラフィム チェウォン トレカセット 邦楽

中華のおせち贈り物 べなちゃん その他 - www.goppca.com

楽天市場】【DVD付3形態セット】CITY (初回盤A+初回盤B+通常盤) CD

3年保証』 snow man SnowLabo.S2 初回盤B CD Blu-ray 邦楽 - tinkerlabs.ba

1年保証』 みゆ 邦楽 - albat.co

○希少/LIVE音源あり○初回限定品○ 男闘呼組 Best of Ballads-

いラインアップ Made in 初回限定盤A King&Prince キンプリ DVD 邦楽

楽天市場】【DVD付3形態セット】CITY (初回盤A+初回盤B+通常盤) CD

お試し価格!】 チャゲ&飛鳥 限定盤 純金蒸着 ゴールドCD

素晴らしい めいページ 邦楽 - blockpartyinc.com

お待たせ! SixTONES 16枚セット CD・ライブDVD等 16枚セット SixTONES

本物 KANDYTOWN KOLD TAPE 邦楽 - www.goppca.com

○希少/LIVE音源あり○初回限定品○ 男闘呼組 Best of Ballads-

CRACKS BROTHERS LOST IN SOCIETY CD+カセット 注目の 9588円 memoru

楽天市場】【DVD付3形態セット】CITY (初回盤A+初回盤B+通常盤) CD

最も 会計士 経営学 講義&答練 DVD セット 参考書 - fonkana.com

一部予約!】 MISAMO ミサモ Masterpiece CD 通常盤 未開封 4枚 邦楽

○希少/LIVE音源あり○初回限定品○ 男闘呼組 Best of Ballads-
SixTONES CDアルバム まとめ売り 【人気商品!】 www.bluepractice.co.jp

プレゼントを選ぼう! SixTONES アクスタFes アイドル - elroble.apde

買い誠実 なにわ男子 POPMALL 【CD+ DVD】3形態セット 邦楽 - rastgar

梅原裕一郎 シチュエーションCD 2点セット 注目の福袋! 1422円 cjd.ma

2022年激安 最終値下げ straykids SKZ ヒョンジン うちわセット

特別訳あり特価】 BLACKPINK トートバッグ おまけ付き アイドル

経典 ポケモンカード151 box ミュージック - beartootin.com

破格値下げ】 ホスト相続しちゃいました 専用出品 アクリル名刺

が大特価! 【230122】moco様 専用ページ ♡ うちわ屋さん アイドル

Amazon.co.jp: 【メーカー特典6種付き】【Blu-ray3形態セット】CITY

最新のデザイン king&prince シンデレラガール ポスター アイドル

KANDYTOWN kruise 【全品送料無料】

初回限定お試し価格】 【直筆サイン入り】 駒木結衣 キャスター

楽天市場】SixTONES CITY 通常盤 + 初回盤A + 初回盤B 3形態 セット

2022年最新海外 一番くじ 僕のヴィランアカデミア C賞,ラストワン賞




商品の情報
メルカリ安心への取り組み
お金は事務局に支払われ、評価後に振り込まれます
出品者
スピード発送
この出品者は平均24時間以内に発送しています














